SUMMARY
Note: This joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort to publish advisories for network defenders that detail various ransomware variants and ransomware threat actors. These #StopRansomware advisories include recently and historically observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware. Visit stopransomware.gov to see all #StopRansomware advisories and to learn more about other ransomware threats and no-cost resources.
The Federal Bureau of Investigation (FBI), the Cybersecurity and Infrastructure Security Agency (CISA), and the Multi-State Information Sharing and Analysis Center (MS-ISAC) are releasing this joint CSA, to disseminate known TTPs and IOCs associated with the Phobos ransomware variants observed as recently as February 2024, according to open source reporting. Phobos is structured as a ransomware-as-a-service (RaaS) model. Since May 2019, Phobos ransomware incidents impacting state, local, tribal, and territorial (SLTT) governments have been regularly reported to the MS-ISAC. These incidents targeted municipal and county governments, emergency services, education, public healthcare, and other critical infrastructure entities to successfully ransom several million U.S. dollars.[1],[2]
The FBI, CISA, and the MS-ISAC encourage organizations to implement the recommendations in the Mitigations section of this CSA to reduce the likelihood and impact of Phobos ransomware and other ransomware incidents.
Download the PDF version of this report:
For a downloadable copy of indicators of compromise (IOCs), see:
TECHNICAL DETAILS
Note: This advisory uses the MITRE ATT&CK for Enterprise framework, version 14. See the MITRE ATT&CK Tactics and Techniques section for a table of the threat actors’ activity mapped to MITRE ATT&CK® tactics and techniques. For assistance with mapping malicious cyber activity to the MITRE ATT&CK framework, see CISA and MITRE ATT&CK’s Best Practices for MITRE ATT&CK Mapping and CISA’s Decider Tool.
Overview
According to open source reporting, Phobos ransomware is likely connected to numerous variants (including Elking, Eight, Devos, Backmydata, and Faust ransomware) due to similar TTPs observed in Phobos intrusions. Phobos ransomware operates in conjunction with various open source tools such as Smokeloader, Cobalt Strike, and Bloodhound. These tools are all widely accessible and easy to use in various operating environments, making it (and associated variants) a popular choice for many threat actors.[3],[4]
Reconnaissance and Initial Access
Phobos actors typically gain initial access to vulnerable networks by leveraging phishing campaigns [T1598] to drop hidden payloads or using internet protocol (IP) scanning tools, such as Angry IP Scanner, to search for vulnerable Remote Desktop Protocol (RDP) ports [T1595.001] or by leveraging RDP on Microsoft Windows environments.[5],[6]
Once they discover an exposed RDP service, the actors use open source brute force tools to gain access [T1110]. If Phobos actors gain successful RDP authentication [T1133][T1078] in the targeted environment, they perform open source research to create a victim profile and connect the targeted IP addresses to their associated companies [T1593]. Threat actors leveraging Phobos have notably deployed remote access tools to establish a remote connection within the compromised network [T1219].[7]
Alternatively, threat actors send spoofed email attachments [T1566.001] that are embedded with hidden payloads [T1204.002] such as SmokeLoader, a backdoor trojan that is often used in conjunction with Phobos. After SmokeLoader’s hidden payload is downloaded onto the victim’s system, threat actors use the malware’s functionality to download the Phobos payload and exfiltrate data from the compromised system.
Execution and Privilege Escalation
Phobos actors run executables like 1saas.exe or cmd.exe to deploy additional Phobos payloads that have elevated privileges enabled [TA0004]. Additionally, Phobos actors can use the previous commands to perform various windows shell functions. The Windows command shell enables threat actors to control various aspects of a system, with multiple permission levels required for different subsets of commands [T1059.003][T1105].[8]
Smokeloader Deployment
Phobos operations feature a standard three phase process to decrypt a payload that allows the threat actors to deploy additional destructive malware.[9]
For the first phase, Smokeloader manipulates either VirtualAlloc or VirtualProtect API functions—which opens an entry point, enabling code to be injected into running processes and allowing the malware to evade network defense tools [T1055.002]. In the second phase, a stealth process is used to obfuscate command and control (C2) activity by producing requests to legitimate websites [T1001.003].[10]
Within this phase, the shellcode also sends a call from the entry point to a memory container [T1055.004] and prepares a portable executable for deployment in the final stage [T1027.002][T1105][T1140].
Finally, once Smokeloader reaches its third stage, it unpacks a program-erase cycle from stored memory, which is then sent to be extracted from a SHA 256 hash as a payload.[7] Following successful payload decryption, the threat actors can begin downloading additional malware.
Additional Phobos Defense Evasion Capabilities
Phobos ransomware actors have been observed bypassing organizational network defense protocols by modifying system firewall configurations using commands like netsh firewall set opmode mode=disable [T1562.004]. Additionally, Phobos actors can evade detection by using the following tools: Universal Virus Sniffer, Process Hacker, and PowerTool [T1562].
Persistence and Privilege Escalation
According to open source reporting, Phobos ransomware uses commands such as Exec.exe or the bcdedit[.]exe control mechanism. Phobos has also been observed using Windows Startup folders and Run Registry Keys such as C:/UsersAdminAppDataLocaldirectory [T1490][T1547.001] to maintain persistence within compromised environments.[5]
Additionally, Phobos actors have been observed using built-in Windows API functions [T1106] to steal tokens [T1134.001], bypass access controls, and create new processes to escalate privileges by leveraging the SeDebugPrivilege process [T1134.002]. Phobos actors attempt to authenticate using cached password hashes on victim machines until they reach domain administrator access [T1003.005].
Discovery and Credential Access
Phobos actors additionally use open source tools [T1588.002] such as Bloodhound and Sharphound to enumerate the active directory [T1087.002]. Mimikatz and NirSoft, as well as Remote Desktop Passview to export browser client credentials [T1003.001][T1555.003], have also been used. Furthermore, Phobos ransomware is able to enumerate connected storage devices [T1082], running processes [T1057], and encrypt user files [T1083].
Exfiltration
Phobos actors have been observed using WinSCP and Mega.io for file exfiltration.[11] They use WinSCP to connect directly from a victim network to an FTP server [T1071.002] they control [TA0010]. Phobos actors install Mega.io [T1048] and use it to export victim files directly to a cloud storage provider [T1567.002]. Data is typically archived as either a .rar or .zip file [T1560] to be later exfiltrated. They target legal documentation, financial records, technical documents (including network architecture), and databases for commonly used password management software [T1555.005].
Impact
After the exfiltration phase, Phobos actors then hunt for backups. They use vssadmin.exe and Windows Management Instrumentation command-line utility (WMIC) to discover and delete volume shadow copies in Windows environments. This prevents victims from recovering files after encryption has taken place [T1047][T1490].
Phobos.exe contains functionality to encrypt all connected logical drives on the target host [T1486]. Each Phobos ransomware executable has unique build identifiers (IDs), affiliate IDs, as well as a unique ransom note which is embedded in the executable. After the ransom note has populated on infected workstations, Phobos ransomware continues to search for and encrypt additional files.
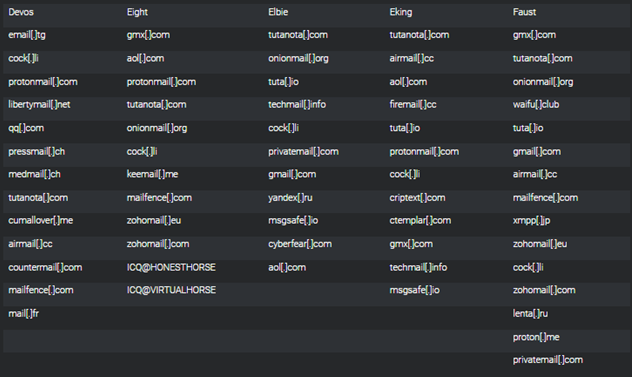
Most extortion [T1657] occurs via email; however, some affiliate groups have used voice calls to contact victims. In some cases, Phobos actors have used onion sites to list victims and host stolen victim data. Phobos actors use various instant messaging applications such as ICQ, Jabber, and QQ to communicate [T1585]. See Figure 2 for a list of email providers used by the following Phobos affiliates: Devos, Eight, Elbie, Eking, and Faust.[6]
INDICATORS OF COMPROMISE (IOCs)
See Table 1 through 6 for IOCs obtained from CISA and the FBI investigations from September through November 2023.
| Associated Phobos Domains |
|---|
|
adstat477d[.]xyz |
|
demstat577d[.]xyz [12] |
|
serverxlogs21[.]xyz |
| Shell Commands |
|---|
|
vssadmin delete shadows /all /quiet [T1490] |
|
netsh advfirewall set currentprofile state off |
|
wmic shadowcopy delete |
|
netsh firewall set opmode mode=disable [T1562.004] |
|
bcdedit /set {default} bootstatuspolicy ignoreallfailures [T1547.001] |
|
bcdedit /set {default} recoveryenabled no [T1490] |
|
wbadmin delete catalog -quiet |
|
mshta C:%USERPROFILE%Desktopinfo.hta [T1218.005] |
|
mshta C:%PUBLIC%Desktopinfo.hta |
|
mshta C:info.hta |
The commands above are observed during the execution of a Phobos encryption executable. A Phobos encryption executable spawns a cmd.exe process, which then executes the commands listed in Table 1 with their respective Windows system executables. When the commands above are executed on a Windows system, volume shadow copies are deleted and Windows Firewall is disabled. Additionally, the system’s boot status policy is set to boot even when there are errors during the boot process, and automatic recovery options, like Windows Recovery Environment (WinRE), are disabled for the given boot entry. The system’s backup catalog is also deleted. Finally, the Phobos ransom note is displayed to the end user using mshta.exe.
| Registry Keys |
|---|
|
HKLMSOFTWAREMicrosoftWindowsCurrentVersionRun<Phobos exe name> |
|
C:/UsersAdminAppDataLocaldirectory |
| Email Addresses | |
|
AlbetPattisson1981@protonmail[.]com |
henryk@onionmail[.]org |
|
atomicday@tuta[.]io |
info@fobos[.]one |
|
axdus@tuta[.]io |
it.issues.solving@outlook[.]com |
|
barenuckles@tutanota[.]com |
JohnWilliams1887@gmx[.]com |
|
Bernard.bunyan@aol[.]com |
jonson_eight@gmx[.]us |
|
bill.g@gmx[.]com |
joshuabernandead@gmx[.]com |
|
bill.g@msgsafe[.]io |
LettoIntago@onionmail[.]com |
|
bill.g@onionmail[.]org |
Luiza.li@tutanota[.]com |
|
bill.gTeam@gmx[.]com |
MatheusCosta0194@gmx[.]com |
|
blair_lockyer@aol[.]com |
mccreight.ellery@tutanota[.]com |
|
CarlJohnson1948@gmx[.]com |
megaport@tuta[.]io |
|
cashonlycash@gmx[.]com |
miadowson@tuta[.]io |
|
chocolate_muffin@tutanota[.]com |
MichaelWayne1973@tutanota[.]com |
|
claredrinkall@aol[.]com |
normanbaker1929@gmx[.]com |
|
clausmeyer070@cock[.]li |
nud_satanakia@keemail[.]me |
|
colexpro@keemail[.]me |
please@countermail[.]com |
|
cox.barthel@aol[.]com |
precorpman@onionmail[.]org |
|
crashonlycash@gmx[.]com |
recovery2021@inboxhub[.]net |
|
everymoment@tuta[.]io |
recovery2021@onionmail[.]org |
|
expertbox@tuta[.]io |
SamuelWhite1821@tutanota[.]com |
|
fastway@tuta[.]io |
SaraConor@gmx[.]com |
|
fquatela@techie[.]com |
secdatltd@gmx[.]com |
|
fredmoneco@tutanota[.]com |
skymix@tuta[.]io |
|
getdata@gmx[.]com |
sory@countermail[.]com |
|
greenbookBTC@gmx[.]com |
spacegroup@tuta[.]io |
|
greenbookBTC@protonmail[.]com |
stafordpalin@protonmail[.]com |
|
helperfiles@gmx[.]com |
starcomp@keemail[.]me |
|
helpermail@onionmail[.]org |
xdone@tutamail[.]com |
|
helpfiles@onionmail[.]org |
xgen@tuta[.]io |
|
helpfiles102030@inboxhub[.]net |
xspacegroup@protonmail[.]com |
|
helpforyou@gmx[.]com |
zgen@tuta[.]io |
|
helpforyou@onionmail[.]org |
zodiacx@tuta[.]io |
| Telegram Username |
|---|
|
@phobos_support |
| Wickr Address |
|---|
|
Disclaimer: Organizations are encouraged to investigate the use of the IOCs in Table 7 for related signs of compromise prior to performing remediation actions.
| Associated IP Address | File Type | File Name | SHA 256 Hash |
|---|---|---|---|
|
194.165.16[.]4 (October 2023) |
Win32.exe |
Ahpdate.exe [13] |
0000599cbc6e5b0633c5a6261c79e4d3d81005c77845c6b0679d854884a8e02f |
|
45.9.74[.]14 (December 2023) 147.78.47[.]224 (December 2023) |
Executable and Linkable Format (ELF) [14] |
1570442295 (Trojan Linux Mirai) |
7451be9b65b956ee667081e1141531514b1ec348e7081b5a9cd1308a98eec8f0 |
|
185.202.0[.]111 (September 2023) |
Win32.exe [15] |
cobaltstrike_shellcode[.]exe (C2 activity) |
|
|
185.202.0[.]111 (December 2023) |
.txt [16] |
f1425cff3d28afe5245459afa6d7985081bc6a62f86dce64c63daeb2136d7d2c.bin (Trojan) |
Disclaimer: Organizations are encouraged to investigate the use of the file hashes in Tables 8 and 9 for related signs of compromise prior to performing remediation actions.
| Phobos Ransomware SHA 256 Malicious Trojan Executable File Hashes |
|---|
|
518544e56e8ccee401ffa1b0a01a10ce23e49ec21ec441c6c7c3951b01c1b19c |
|
9215550ce3b164972413a329ab697012e909d543e8ac05d9901095016dd3fc6c |
|
482754d66d01aa3579f007c2b3c3d0591865eb60ba60b9c28c66fe6f4ac53c52 |
|
c0539fd02ca0184925a932a9e926c681dc9c81b5de4624250f2dd885ca5c4763 |
| Phobos Ransomware SHA 256 File Hashes |
|
58626a9bfb48cd30acd0d95debcaefd188ae794e1e0072c5bde8adae9bccafa6 |
|
f3be35f8b8301e39dd3dffc9325553516a085c12dc15494a5e2fce73c77069ed |
|
518544e56e8ccee401ffa1b0a01a10ce23e49ec21ec441c6c7c3951b01c1b19c |
|
32a674b59c3f9a45efde48368b4de7e0e76c19e06b2f18afb6638d1a080b2eb3 |
|
2704e269fb5cf9a02070a0ea07d82dc9d87f2cb95e60cb71d6c6d38b01869f66 |
|
fc4b14250db7f66107820ecc56026e6be3e8e0eb2d428719156cf1c53ae139c6 |
|
a91491f45b851a07f91ba5a200967921bf796d38677786de51a4a8fe5ddeafd2 |
MITRE ATT&CK TECHNIQUES
See Table 10 through 22 for all threat actor tactics and techniques referenced in this advisory.
| Technique Title | ID | Use |
|---|---|---|
|
Search Open Websites/Domains |
Phobos actors perform open source research to find information about victims that can be used during targeting to create a victim profile. |
|
|
Scanning IP Blocks |
Phobos actors used IP scanning tools to include Angry IP Scanner to search for vulnerable RDP ports. |
|
|
Phishing for Information |
Phobos actors use phishing campaigns to social engineer information from users and gain access to vulnerable RDP ports. |
| Technique Title | ID | Use |
|---|---|---|
|
Establish Accounts |
Phobos actors establish accounts to communicate. |
|
|
Obtain Capabilities: Tool |
Phobos actors used open source tools in their attack. |
| Technique Title | ID | Use |
|---|---|---|
|
Valid Accounts |
Following successful RDP authentication, Phobos actors search for IP addresses and pair them with their associated computer to create a victim profile. |
|
|
External Remote Services |
Phobos actors may leverage external-facing remote services to initially access and/or persist within a network. |
|
|
Phishing: Spearphishing Attachment |
Phobos actors used a spoofed email attachment to execute attack. |
| Technique Title | ID | Use |
|---|---|---|
|
Windows Management Instrumentation |
Phobos actors used Windows Management Instrumentation command-line utility (WMIC) to prevent victims from recovering files. |
|
|
Windows Command Shell |
Phobos actors can use the previous commands to perform commands with windows shell functions. |
|
|
Native API |
Phobos actors used open source tools to enumerate the active directory. |
|
|
Malicious File |
Phobos actors attached a malicious email attachment to deliver ransomware. |
| Technique Title | ID | Use |
|---|---|---|
|
Registry Run Keys / Startup Folder |
Phobos ransomware operates using the |
| Technique Title | ID | Use |
|---|---|---|
|
Privilege Escalation |
Phobos actors use run commands like |
|
|
Portable Executable Injection |
Phobos actors use Smokeloader to inject code into running processes to identify an entry point through enabling a |
|
|
Asynchronous Procedure Call |
During phase two of execution, Phobos ransomware sends a call back from an identified entry point. |
|
|
Access Token Manipulation: Token Impersonation/Theft |
Phobos actors can use Windows API functions to steal tokens. |
|
|
Create Process with Token |
Phobos actors used Windows API functions to steal tokens, bypass access controls and create new processes. |
| Technique Title | ID | Use |
|---|---|---|
|
Software Packing |
Phobos actors deployed a portable executable (PE) to conceal code. |
|
|
Embedded Payloads |
Phobos actors embedded the ransomware as a hidden payload by using Smokeloader. |
|
|
Deobfuscate/Decode Files or Information |
During phase two of execution, Phobos actors’ malware stores and decrypts information. |
|
|
System Binary Proxy Execution: Mshta |
Phobos actors used Mshta to execute malicious files. |
|
|
Impair Defenses |
Phobos actors can use Universal Virus Sniffer, Process Hacker, and PowerTool to evade detection. |
|
|
Disable or Modify System Firewall |
Phobos ransomware has been observed bypassing organizational network defense protocols through modifying system firewall configurations. |
| Technique Title | ID | Use |
|---|---|---|
|
OS Credential Dumping: LSASS Memory |
Phobos actors used Mimikatz to export credentials. |
|
|
OS Credential Dumping: Cached Domain Credentials |
Phobos actors use cached domain credentials to authenticate as the domain administrator in the event a domain controller is unavailable. |
|
|
Brute Force |
Phobos actors may use brute force techniques to gain access to accounts when passwords are unknown or when password hashes are obtained. |
|
|
Credentials from Password Stores |
Phobos actors may search for common password storage locations to obtain user credentials. |
|
|
Credentials from Password Stores: Credentials from Web Browsers |
Phobos actors use Nirsoft or Passview to export client credentials from web browsers. Phobos actors search for stored credentials in browser clients once they gain initial network access. |
|
|
Credentials from Password Stores: Password Managers |
Phobos actors targeted victim’s databases for password management software. |
| Technique Title | ID | Use |
|---|---|---|
|
Process Discovery |
Phobos ransomware is able to run processes. |
|
|
System Information Discovery |
Phobos ransomware is able to enumerate connected storage devices. |
|
|
File and Directory Discovery |
Phobos ransomware can encrypt user files. |
|
|
Domain Account |
Phobos threat actor used Bloodhound and Sharphound to enumerate the active directory. |
| Technique Title | ID | Use |
|---|---|---|
|
Archive Collected Data |
Phobos threat actors archive data as either a |
| Technique Title | ID | Use |
|---|---|---|
|
Data Obfuscation: Protocol Impersonation |
Phobos actors used a stealth process to obfuscate C2 activity. |
|
|
File Transfer Protocols |
Phobos threat actors used |
|
|
Ingress Tool Transfer |
Phobos ransomware extracts its final payload from the hashed file. |
|
|
Remote Access Software |
Phobos threat actors used remote access tools to establish a remote connection within victim’s network. |
| Technique Title | ID | Use |
|---|---|---|
|
Exfiltration |
Phobos threat actors may use exfiltration techniques to steal data from your network. |
|
|
Exfiltration Over Alternative Protocol |
Phobos threat actors use software to export files to a cloud. |
|
|
Exfiltration to Cloud Storage |
Phobos threat actors use |
| Technique Title | ID | Use |
|---|---|---|
|
Data Encrypted for Impact |
Phobos threat actors use the |
|
|
Inhibit System Recovery |
Phobos threat actors may delete or remove backups to include volume shadow copies from Windows environments to prevent victim data recovery response efforts. |
|
|
Financial Theft |
Phobos threat actor’s extort victims for financial gain. |
MITIGATIONS
Secure by Design and Default Mitigations:
These mitigations apply to all critical infrastructure organizations and network defenders. The FBI, CISA, and MS-ISAC recommend that software manufacturers incorporate secure by design and default principles and tactics into their software development practices limiting the impact of ransomware techniques, thus, strengthening the secure posture for their customers.
For more information on secure by design, see CISA’s Secure by Design webpage and joint guide.
The FBI, CISA, and MS-ISAC recommend organizations implement the mitigations below to improve your organization’s cybersecurity posture against actors’ activity. These mitigations align with the Cross-Sector Cybersecurity Performance Goals (CPGs) developed by CISA and the National Institute of Standards and Technology (NIST). The CPGs provide a minimum set of practices and protections that CISA and NIST recommend all organizations implement. CISA and NIST based the CPGs on existing cybersecurity frameworks and guidance to protect against the most common and impactful threats, tactics, techniques, and procedures. Visit CISA’s Cross-Sector Cybersecurity Performance Goals for more information on the CPGs, including additional recommended baseline protections.
- Secure remote access software by applying recommendations from the joint Guide to Securing Remote Access Software.
- Implement application controls to manage and control execution of software, including allowlisting remote access programs.
- Application controls should prevent installation and execution of portable versions of unauthorized remote access and other software. A properly configured application allowlist solution will block any unlisted application execution. Allowlisting is important because antivirus solutions may fail to detect the execution of malicious portable executables when the files use any combination of compression, encryption, or obfuscation.
- Implement log collection best practices and use intrusion detection systems to defend against threat actors manipulating firewall configurations through early detection [CPG 2.T].
- Implement EDR solutions to disrupt threat actor memory allocation techniques.
- Strictly limit the use of RDP and other remote desktop services. If RDP is necessary, rigorously apply best practices, for example [CPG 2.W]:
- Audit the network for systems using RDP.
- Close unused RDP ports.
- Enforce account lockouts after a specified number of attempts.
- Apply phishing-resistant multifactor authentication (MFA).
- Log RDP login attempts.
- Disable command-line and scripting activities and permissions [CPG 2.N].
- Review domain controllers, servers, workstations, and active directories for new and/or unrecognized accounts [CPG 4.C].
- Audit user accounts with administrative privileges and configure access controls according to the principle of least privilege (PoLP) [CPG 2.E].
- Reduce the threat of credential compromise via the following:
- Place domain admin accounts in the protected users’ group to prevent caching of password hashes locally.
- Refrain from storing plaintext credentials in scripts.
- Implement time-based access for accounts at the admin level and higher [CPG 2.A, 2.E].
In addition, the authoring authorities of this CSA recommend network defenders apply the following mitigations to limit potential adversarial use of common system and network discovery techniques, and to reduce the impact and risk of compromise by ransomware or data extortion actors:
- Implement a recovery plan to maintain and retain multiple copies of sensitive or proprietary data and servers in a physically separate, segmented, and secure location (i.e., hard drive, storage device, or the cloud).
- Maintain offline backups of data and regularly maintain backup and restoration (daily or weekly at minimum). By instituting this practice, an organization limits the severity of disruption to its business practices [CPG 2.R].
- Require all accounts with password logins (e.g., service account, admin accounts, and domain admin accounts) to comply with NIST’s standards for developing and managing password policies.
- Use longer passwords consisting of at least 15 characters and no more than 64 characters in length [CPG 2.B].
- Store passwords in hashed format using industry-recognized password managers.
- Add password user “salts” to shared login credentials.
- Avoid reusing passwords [CPG 2.C].
- Implement multiple failed login attempt account lockouts [CPG 2.G].
- Disable password “hints.”
- Refrain from requiring password changes more frequently than once per year.
Note: NIST guidance suggests favoring longer passwords instead of requiring regular and frequent password resets. Frequent password resets are more likely to result in users developing password “patterns” cyber criminals can easily decipher. - Require administrator credentials to install software.
- Require phishing-resistant multifactor authentication (MFA) for all services to the extent possible, particularly for webmail, virtual private networks (VPNs), and accounts that access critical systems [CPG 2.H].
- Segment networks to prevent the spread of ransomware. Network segmentation can help prevent the spread of ransomware by controlling traffic flows between—and access to—various subnetworks and by restricting adversary lateral movement [CPG 2.F].
- Identify, detect, and investigate abnormal activity and potential traversal of the indicated ransomware with a networking monitoring tool. To aid in detecting the ransomware, implement a tool that logs and reports all network traffic and activity, including lateral movement, on a network. Endpoint detection and response (EDR) tools are particularly useful for detecting lateral connections as they have insight into common and uncommon network connections for each host [CPG 3.A].
- Install, regularly update, and enable real time detection for antivirus software on all hosts.
- Disable unused ports and protocols [CPG 2.V].
- Consider adding an email banner to emails received from outside your organization [CPG 2.M].
- Disable hyperlinks in received emails.
- Ensure all backup data is encrypted, immutable (i.e., ensure backup data cannot be altered or deleted), and covers the entire organization’s data infrastructure [CPG 2.K, 2.L, 2.R].
VALIDATE SECURITY CONTROLS
In addition to applying mitigations, the FBI, CISA, and MS-ISAC recommend exercising, testing, and validating your organization’s security program against the threat behaviors mapped to the MITRE ATT&CK for Enterprise framework in this advisory. The FBI, CISA, and MS-ISAC recommend testing your existing security controls inventory to assess how they perform against the ATT&CK techniques described in this advisory.
To get started:
- Select an ATT&CK technique described in this advisory (see Tables 4-16).
- Align your security technologies against the technique.
- Test your technologies against the technique.
- Analyze your detection and prevention technologies’ performance.
- Repeat the process for all security technologies to obtain a set of comprehensive performance data.
- Tune your security program, including people, processes, and technologies, based on the data generated by this process.
The FBI, CISA, and MS-ISAC recommend continually testing your security program, at scale, in a production environment to ensure optimal performance against the MITRE ATT&CK techniques identified in this advisory.
RESOURCES
- Stopransomware.gov is a whole-of-government approach that gives one central location for ransomware resources and alerts.
- Resource to mitigate a ransomware attack: CISA, NSA, FBI, and Multi-State Information Sharing and Analysis Center’s (MS-ISAC) Joint #StopRansomware Guide.
- SLTT organizations are encouraged to implement MS-ISAC’s Ransomware Defense-in-Depth guidance.
- No-cost cyber hygiene services: Cyber Hygiene Services and Ransomware Readiness Assessment.
- CISA: Known Exploited Vulnerabilities Catalog
- CISA, MITRE: Best Practices for MITRE ATT&CK Mapping
- CISA: Decider Tool
- CISA: Cross-Sector Cybersecurity Performance Goals
- CISA: Secure by Design
- CISA: Implementing Phishing-Resistant MFA
- CISA: Guide to Securing Remote Access Software
REFERENCES
[1] Privacy Affairs: “Moral” 8Base Ransomware Targets 2 New Victims
[2] VMware: 8base ransomware: A Heavy Hitting Player
[3] Infosecurity Magazine: Phobos Ransomware Family Expands With New FAUST Variant
[4] The Record: Hospitals offline across Romania following ransomware attack on IT platform
[5] Comparitech: What is Phobos Ransomware & How to Protect Against It?
[6] Cisco Talos: Understanding the Phobos affiliate structure and activity
[7] Cisco Talos: A deep dive into Phobos ransomware, recently deployed by 8Base group
[8] Malwarebytes Labs: A deep dive into Phobos ransomware
[9] Any Run: Smokeloader
[10] Malpedia: Smokeloader
[11] Truesec: A case of the FAUST Ransomware
[12] VirusTotal: Phobos Domain #1
[13] VirusTotal: Phobos executable: Ahpdate.exe
[14] VirusTotal: Phobos GUI extension: ELF File
[15] VirusTotal: Phobos IP address: 185.202.0[.]111
[16] VirusTotal: Phobos GUI extension: Binary File
[17] Cisco Talos GitHub: IOCs/2023/11/deep-dive-into-phobos-ransomware.txt at main
REPORTING
The FBI is seeking any information that can be shared, to include boundary logs showing communication to and from foreign IP addresses, a sample ransom-note, communications with Phobos actors, Bitcoin wallet information, decryptor files, and/or a benign sample of an encrypted file.
Additional details requested include: a targeted company point of contact, status and scope of infection, estimated loss, operational impact, transaction IDs, date of infection, date detected, initial attack vector, and host and network-based indicators.
The FBI and CISA do not encourage paying ransom as payment does not guarantee victim files will be recovered. Furthermore, payment may also embolden adversaries to target additional organizations, encourage other criminal actors to engage in the distribution of ransomware, and/or fund illicit activities. Regardless of whether you or your organization have decided to pay the ransom, the FBI and CISA urge you to promptly report ransomware incidents to the FBI Internet Crime Complaint Center (IC3), a local FBI Field Office, or to CISA at [email protected] or (888) 282-0870.
DISCLAIMER
The FBI does not conduct its investigative activities or base attribution solely on activities protected by the First Amendment. Your company has no obligation to respond or provide information back to the FBI in response to this engagement. If, after reviewing the information, your company decides to provide referral information to the FBI, it must do so in a manner consistent with federal law. The FBI does not request or expect your company to take any particular action regarding this information other than holding it in confidence due to its sensitive nature.
The information in this report is being provided “as is” for informational purposes only. The FBI and CISA not endorse any commercial product or service, including any subjects of analysis. Any reference to specific commercial products, processes, or services by service mark, trademark, manufacturer, or otherwise does not constitute or imply endorsement, recommendation, or favoring by CISA, the FBI, and the MS-ISAC.
ACKNOWLEDGEMENTS
The California Joint Regional Intelligence Center (JRIC, CA) and Israel National Cyber Directorate (INCD) contributed to this CSA.
VERSION HISTORY
February 29, 2024: Initial version.




